~wired | Bookmarks (134)
-
Roku Breach Hits 567,000 Users
Plus: Apple warns iPhone users about spyware attacks, CISA issues an emergency directive about a Microsoft...
-
House Votes to Extend—and Expand—a Major US Spy Program
The US House of Representatives voted on Friday to extend the Section 702 spy program. It...
-
Change Healthcare Faces Another Ransomware Threat—and It Looks Credible
Change Healthcare ransomware hackers already received a $22 million payment. Now a second group is demanding...
-
The Best Personal Safety Devices, Apps, and Wearables
Your smartphone or wearable could help you out in a truly dangerous situation. Here are some...
-
DuckDuckGo Is Taking Its Privacy Fight to Data Brokers
Privacy-focused company DuckDuckGo is launching a tool to remove data from people-search websites, a VPN, and...
-
Trump Loyalists Kill Vote on US Wiretap Program
An attempt to reauthorize Section 702, the so-called crown jewel of US spy powers, failed for...
-
How to Stop Your Data From Being Used to Train AI
Some companies let you opt out of allowing your content to be used for generative AI....
-
How to Protect Yourself (and Your Loved Ones) From AI Scam Calls
AI tools are getting better at cloning people’s voices, and scammers are using these new capabilities...
-
It's Time to Switch to a Privacy Browser
Ad trackers are out of control. Use a browser that reins them in.
-
Identity Thief Lived as a Different Man for 33 Years
Plus: Microsoft scolded for a “cascade” of security failures, AI-generated lawyers send fake legal threats, a...
-
A Vigilante Hacker Took Down North Korea’s Internet. Now He’s Taking Off His Mask
As “P4x,” Alejandro Caceres single-handedly disrupted the internet of an entire country. Then he tried to...
-
The Mystery of ‘Jia Tan,’ the XZ Backdoor Mastermind
The thwarted XZ Utils supply chain attack was years in the making. Now, clues suggest nation-state...
-
The XZ Backdoor: Everything You Need to Know
Details are starting to emerge about a stunning supply chain attack that sent the open source...
-
The Incognito Mode Myth Has Fully Unraveled
To settle a years-long lawsuit, Google has agreed to delete “billions of data records” collected from...
-
How a Houthi-Bombed Ghost Ship Likely Cut Off Internet for Millions
Millions lost internet service after three cables in the Red Sea were damaged. Houthi rebels deny...
-
You Should Update Apple iOS and Google Chrome ASAP
Plus: Microsoft patches over 60 vulnerabilities, Mozilla fixes two Firefox zero-day bugs, Google patches 40 issues...
-
Yogurt Heist Reveals a Rampant Form of Online Fraud
Plus: “MFA bombing” attacks target Apple users, Israel deploys face recognition tech on Gazans, AI gets...
-
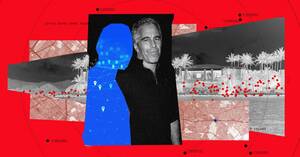
Jeffrey Epstein's Island Visitors Exposed by Data Broker
A WIRED investigation uncovered coordinates collected by a controversial data broker that reveal sensitive information about...
-
‘Malicious Activity’ Hits the University of Cambridge’s Medical School
Multiple university departments linked to the Clinical School Computing Service have been inaccessible for a month....
-
Judges Block US Extradition of WikiLeaks Founder Julian Assange—for Now
A high court in London says the WikiLeaks founder won’t be extradited “immediately” and the US...
-
Chinese Hackers Charged in Decade-Long Global Spying Rampage
US and UK officials hit Chinese hacking group APT31 with sanctions and criminal charges after they...
-
Apple Chip Flaw Leaks Secret Encryption Keys
Plus: The Biden administration warns of nationwide attacks on US water systems, a new Russian wiper...
-
The DOJ Puts Apple's iMessage Encryption in the Antitrust Crosshairs
Privacy and security are an Apple selling point. But the DOJ’s new antitrust lawsuit argues that...
-
Hackers Found a Way to Open Any of 3 Million Hotel Keycard Locks in Seconds
The company behind the Saflok-brand door locks is offering a fix, but it may take months...