~hackernoon | Bookmarks (1964)
-
AI-Augmented Development: Redefining the Role of Product Managers
AI-assisted design and development tools are democratizing the product development process. Platforms like OpenAI's Playground, n8n,...
-
DWF Ventures Analyzes Impact of $TRUMP Memecoin Surge on Crypto Markets
Two days before the inauguration, $TRUMP memecoin was introduced into the crypto market. The token’s market...
-
NestJS Too Slow? Just Queue It!
Processing resource-intensive tasks, like file uploads or report generation, can bog down a NestJS application, leading...
-
Knowing 'When' to Switch: A Glimpse into the Future of Pattern Matching
An overview of the when statement: a flexible pattern matching structure in DeltaScript, and an alternative...
-
For Spacecoin to Truly Differentiate Itself, it Must Move Beyond Corporate Decision-making Models
While Spacecoin's vision of combining satellite networks with blockchain technology shows immense promise, its true potential...
-
This 7-Step Framework Guided Me to $300K in Monthly Revenue
We've just hit $30K per month in revenue for a product launched only 10 months ago....
-
Previously Undisclosed Flaw Let Hackers Hijack Millions of Systems Through Innocent-Looking Files
Zip Slip is a serious vulnerability that is widespread in the archive extraction process. The vulnerability...
-
Businesses Are Ditching Big GenAI Overhauls for Smarter, Low-Risk Upgrades
Businesses are pivoting from massive overhauls to smaller, strategic applications of GenAI. The goal is to...
-
The Age of Marketing Funnels is Over
The traditional funnel assumes all leads are equal, ignoring the nuances of behavior, intent, and context....
-
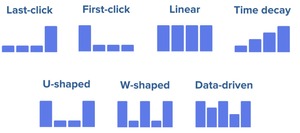
BigQuery and Attribution Models Can Reveal What Really Drives E-Commerce Success
Attribution models play a critical role in the digital marketing and ecommerce world by helping us...
-
Latest Bun Update Brings Performance Improvements
Bun 1.2 is making headlines in the JavaScript runtime scene, pushing the boundaries of Node.js compatibility...
-
Aspect Oriented Programming Matters More Than You Think
AOP is useful in tackling cross cutting concerns which are fully incorporated in the development of...
-
The Surprisingly Weird Tech Making Drones Fly Smarter and Students Learn Faster
Fuzzy logic is a viable and practical form of machine intelligence that has been especially successful...
-
DeepSeek Releases Cheapest Ever LLM In The World
In this edition of This Week in AI Engineering, we go through the latest updates along...
-
Bug Resolution Is So Much Better With Log Analysis
Google Log Explorer is a tool to help you troubleshoot problems in the cloud. It is...
-
Bitcoin Can't Be Explained Over a Coffee Chat
Asking to understand Bitcoin and Blockchain technologies is a testament to the need for deeper understanding...
-
Tracking Other Traders’ Moves Can Save Your Crypto Portfolio
When trading cryptocurrency derivatives, you can use tools such as Open Interest, Funding Rates, Liquidations, or...
-
The HackerNoon Newsletter: Most Concerns About Bitcoin Are Deeply Human (1/27/2025)
How are you, hacker? 🪐 What’s happening in tech today, January 27, 2025? The HackerNoon Newsletter...
-
HackerNoon Decoded 2024: Celebrating Our Gaming Community!
Welcome to HackerNoon Decoded—the ultimate recap of the Gaming stories, writers, and trends that defined 2024!...
-
Regionalize APIs Like a Pro: Achieve Global Compliance and Scalability
Discover how to build APIs that thrive globally! Learn real-world strategies for API regionalization—parameterized endpoints, region-aware...
-
Meet Maruti Techlabs: HackerNoon Company of the Week
Welcome to another Company of the Week feature! Each week, we highlight an innovative business from...
-
Data-driven Autonomous Driving: AI Needs Diverse Training Datasets to Ensure Security and Robustness
The global autonomous vehicle market is expected to grow from USD 1,921.1 billion in 2023 to...
-
Utilitarianism Meets Surveillance Capitalism: Balancing Happiness & Privacy
Utilitarianism weighs surveillance capitalism’s gains in happiness against privacy risks, stressing transparency and oversight for ethical...
-
The Rise of Manipulative Surveillance
This research exposes how targeted ads and military technologies exploit personal data, fueling manipulation, privacy risks,...