~hackernoon | Bookmarks (42)
-
The Journey into Digital Forensics: Exploring Career Opportunities (Revealing Insights)
Discover career opportunities, essential skills, and real-world applications as I explore the critical role of digital...
-
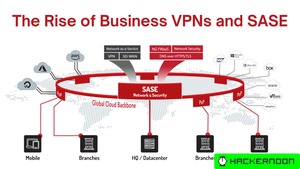
The Rise of Business VPNs and SASE: Securing the Evolving Enterprise Landscape
As businesses increasingly rely on cloud-based resources and remote workforces, the need for robust security solutions...
-
Beyond Encryption: The Expanding Role of VPNs in Cybersecurity
The Virtual Private Network, or VPN, is like a virtual cloak around your data. It encrypts...
-
TeKnowledge's Expansion: Tackling the Tech Talent Crisis with Unified Cybersecurity and Upskilling
TeKnowledge has unifiied the capabilities of Cytek Security, Tek Experts, and Elev8 to expand services. The...
-
Center Identity Launches Patented Passwordless Authentication For Businesses
Center Identity unveils its patented secret location authentication. The technology enables users to authenticate their identity...
-
Bootcamp to Code: US Marine Corps Wisdom for the Tech World
In tech, as in many domains, there's no need to start from scratch. Often, we can...
-
Exposing the Dangerous CAT Command's Limitations in Script Review
By default, the default cat command doesn't display escaped characters, hidden characters, and other non-printable characters...
-
Innovation vs. Security: CISOs Leading the Charge in the Balancing Act of AI
The role of a Chief Information Security Officer (CISO) evolved from IT gatekeepers to business enablers...
-
Empowering Nigeria With Web3: Exploring Autonomy, Cryptocurrency, and DAOs as Pathways to Prosperity
Nigerians have been held down by a corrupt, tyrannical government that seemingly would prefer to keep...
-
Why Cybersecurity for Solar Is Crucial — And Difficult
Because solar infrastructure provides essential services and is often run by government entities, it experiences a...
-
Lessons Learned From the Change Healthcare Cyberattack
The Change Healthcare cyberattack has continued to make waves for physicians and patients. The ramifications of...
-
MDR Provider Checklist: A Useful Guide
Managed detection and response (MDR) solutions are useful tools for organizations that cannot or don’t want...
-
Chrome Password Manager Betrayed My Trust 13 Years Ago. I Never Forgot.
Disillusionment with Chrome's password storage leads to a 13-year journey to create a better password manager....
-
So, You Want to Be a Hacker?
This article promotes entry into Capture The Flag (CTF) competitions for beginners interested in cybersecurity and...
-
Two Years On: How Ukraine's Cyber Warfront Is Redefining Global Cybersecurity Strategies
The Russian war against Ukraine has escalated into the most extensive use of cyber operations in...
-
Deepfake Phishing Grew by 3,000% in 2023 — And It's Just Beginning
Deepfake phishing uses AI-generated content to craft more believable phishing attempts — and these attempts rose...
-
6 Skills You Need to Succeed In Cybersecurity
Cyber Security is a popular field with lots of employment options, competitive salary and a vibrant...
-
Insider Threats are Increasingly Using Privilege Escalation Exploits
A new report may indicate that insider threats are finding new innovative ways to attack core...