~hackernoon | Bookmarks (1966)
-
Chameleon AI Shows Competitive Edge Over LLaMa-2 and Other Models
Chameleon’s AI models outperform LLaMa-2 and match or exceed top models like Mixtral in text benchmarks...
-
The TechBeat: IPinfo Launches IPinfo Lite: Unlimited Country-Level Geolocation API & Database Download (5/20/2025)
How are you, hacker? 🪐Want to know what's trending right now?: The Techbeat by HackerNoon has...
-
Improved BGPLVM for scRNA-seq: Pre-Processing and Likelihood
Learn about the key modifications to the baseline BGPLVM model for single-cell RNA-seq, including library normalization...
-
Encoding Biological Knowledge in GPLVM Kernels for scRNA-seq
Learn how specialized kernel designs in GPLVMs can incorporate prior biological knowledge, like batch effects and...
-
GPLVM for Single-Cell RNA-seq Dimensionality Reduction
Learn about using Gaussian Process Latent Variable Models (GPLVMs) for probabilistic dimensionality reduction of single-cell RNA-seq...
-
Scalable & Interpretable Dimensionality Reduction for scRNA-seq
Discover our improved BGPLVM for single-cell RNA-seq, offering scalable dimensionality reduction with interpretable incorporation of biological...
-
Fighting Piracy With SEO: How I’m Turning Malware Traffic Into Safer Gaming Choices
I stumbled upon something both intriguing and concerning—a network of piracy-promoting websites distributing malware under the...
-
Karthik Chava Proposes Neuro-Symbolic Platforms for Personalized Healthcare
AI expert Karthik Chava introduces neuro-symbolic platforms that fuse logic and learning to advance personalized healthcare....
-
Driving Supply Chain Resilience through AI-Driven Data Synchronization
Avinash Pamisetty outlines how AI-driven data synchronization transforms fragmented supply chains into intelligent, adaptive systems. By...
-
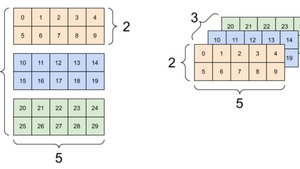
There’s No TensorFlow Without Tensors
Tensors are multi-dimensional arrays at the core of TensorFlow, enabling efficient data representation and manipulation. This...
-
What Sam Altman’s World Network Gets Wrong About Privacy – And What We Can Do Better
Worldcoin, now World Network, faces global scrutiny over its biometric data collection model as it prepares...
-
Is the Time Ripe for a Meta Blockchain to Rule Them All?
Solana’s Anatoly Yakovenko sparks debate with his vision of a ‘meta blockchain’—a unified ledger that merges...
-
How Aliyyah Koloc Is Using Blockchain to Redefine Racing, Identity, & Global Art Access
From the Taklimakan Rally to the art world, Aliyyah Koloc merges speed, heritage, and technology to...
-
Meet the HackerNoon Top Writers - Laszlo Fazekas and Kindness In Content Writing
Meet HackerNoon Top Writer Laszlo Fazekas and explore his writing journey through creativity, kindness, and small,...
-
Comparing Chameleon with GPT-4V and Gemini
Chameleon, a new multimodal AI, was tested against GPT-4V and Gemini using real-world prompts. It consistently...
-
AI Can Code Your App—Just Don’t Let It Architect It
AI coding agents can transform the software development process by reducing development time and allowing for...
-
The Complete Guide to Crafting Security Headlines That Cut Through the Noise
Learn how to write cybersecurity blog titles that grab attention, earn clicks, and build trust—without using...
-
Your Next Data Breach Might Start with a Friendly Face
Insider threats can cost companies millions in data loss, downtime, and reputation. Learn how to detect,...
-
IPinfo’s Free IP Geolocation API Is a Must-Have for Cybersecurity Teams
IPinfo's new free plan gives unlimited IP geolocation and ASN data—perfect for OSINT, threat hunting, log...
-
MCP Servers Still Run Critical Infrastructure—Here’s How to Secure Them
If you're curious about what MCP servers are and why they're important for cybersecurity, you're not...
-
Understanding React Rendering Without the Buzzwords
React is often praised for being “declarative,” “efficient,” and “component-based.” But those words don’t mean much...
-
Card Declines are a Data Problem (But AI Could Fix That!)
In Part 1 of my series, we saw how declines grow from vague issuer responses, outdated...
-
Kubernetes Liveness, Readiness, and Startup Probes – Keys to Container Health and Resilience
Learn how to configure Kubernetes liveness, readiness, and startup probes with real-world examples, YAML configurations, and...
-
7 Cap Table Mistakes That Kill Startups
Your cap table isn’t just a spreadsheet - it’s your ownership, control, and future funding compressed...