Explore
XZ Utils review notes
Trivial commits like updates to THANKS or typo fixes in comments aren’t mentioned here. The months...
Root Cause vs. Contributing Factors
In multiplication, to get a non-zero product, all factors must be greater than 0. If one...
Home
Docs Read more details about CIPHERLEAKs. Q&A Who is affected by CIPHERLEAKs?All SEV, SEV-ES and SEV-SNP...
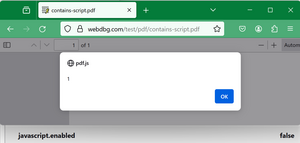
Browser Security Bugs that Aren’t: JavaScript in PDF
A fairly common security bug report is of the form: “I can put JavaScript inside a...
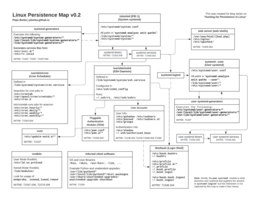
Hunting for Persistence in Linux (Part 1): Auditd, Sysmon, Osquery (and Webshells)
Welcome to this blog series “Hunting for Persistence in Linux”! This is a series that explores...

Putting an xz Backdoor Payload in a Valid RSA Key
Last week, a backdoor was discovered in xz-utils. The backdoor processes commands sent using RSA public...
Kobold letters – Lutra Security
Anyone who has had to deal with HTML emails on a technical level has probably reached...