Explore
Formal Mechanised Semantics of CHERI C: Capabilities, Undefined Behaviour
Memory safety issues are a persistent source of security vulnerabilities, with conventional architectures and the C...
Specifying the Power and Limitations of Randomness
Drawn to computer science at the suggestion of his parents—who thought the field might provide a...
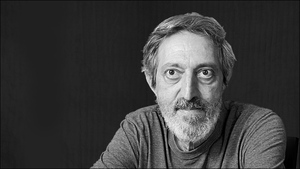
2023 ACM Turing Prize awarded to Avi Wigderson
ACM has named Avi Wigderson as recipient of the 2023 ACM A.M. Turing Award for foundational...
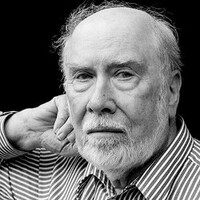
In Memoriam: Ross Anderson, 1956-2024
Ross Anderson unexpectedly passed away in his sleep on March 28th in his home in Cambridge....
Survey of Distributed File System Design Choices | ACM Transactions on Storage
Skip Abstract SectionDecades of research on distributed file systems and storage systems exists. New researchers and...

Communications of the ACM Relaunched as Open Access, Web-First Publication
New York, NY, March 12, 2023 – ACM, the Association for Computing Machinery, has relaunched Communications...
Immutability Changes Everything (2016)
January 20, 2016Volume 13, issue 9 PDF We need it, we can afford it, and the...
Edge AI devices eye lifetime learning
Today, artificial intelligence (AI) devices at the network’s edge—such as the billions of Internet of Things...
Computing Without Processors
From the programmer’s perspective the distinction between hardware and software is being blurred. As programmers struggle...
In Memoriam: Niklaus Wirth
Computing Pioneer Niklaus Wirth died on January 1, 2024, just 45 days short of his 90th...

Co-Developing Programs and Their Proof of Correctness
Credit: Balein / Shutterstock Twenty years ago, Sir Tony Hoare proposed a grand challenge to the...
What DNS Is Not (2009)
November 5, 2009Volume 7, issue 10 PDF What DNS Is Not Paul Vixie, Internet Systems Consortium...
Patent Absurdity
Kode Vicious - @kode_vicious September 29, 2021Volume 19, issue 4 PDF Kode Vicious A case when...




